A blog where I rambles about cybersecurity and other things. Most of it makes sense, but some might not.

How to Secure your Accounts Online
Lately I have sat down to talk with a couple of different groups of people working outside of tech. As someone working with cybersecurity there was a set of statements where I had to interject. This post is a result of these discussions, with the aim to be a reference that can be used to improve the security of everyone, no great technical skills required. I will focus on how we secure our accounts, focusing on the login experience. ...

Is AI Taking the Jobs of Developers?
In this world of AI, no-one can miss the discussions about “vibe coding”. What that means is a the use of AI to write code to develop a product quickly, and the author doesn’t even need to know how to write code. This opens up so many possibilities, as long as the code has a high quality. I won’t dig deeply into the quality of the code produced by AI today, but for now I wouldn’t trust code written by AI to be run in production without rigorous code review and testing. However, if we assume that AI in the future would be of a quality high enough to be run, what would the impact be on Developers? I would argue that this is not a new problem, but a new version of an old problem. ...

Kinds of Penetrationtesting
As a penetration tester, you will inevitably find yourself involved in scoping engagements, navigating the challenges of aligning a client’s needs with their expectations. “Penetration testing” is a term that almost everyone believes they understand, yet it often carries vastly different interpretations. This ambiguity makes it more of an umbrella term, offering little insight into how the test will actually be executed or what it will cover. In this post, I’ll share my perspective on one approach to differentiating how penetration tests can be executed, helping both testers and clients clarify their expectations. ...

Supply Chain Security in Light of EU Regulations: A Practical Approach
Lately, I’ve been thinking about the complexity of securing the software supply chain. If there’s one lesson we’ve learned from incidents like the SolarWinds and Kaseya attacks, it’s that our supply chains are increasingly becoming the weakest link in our cybersecurity defenses. What makes it even more challenging is the regulatory landscape—particularly within the European Union (EU)—which is evolving to place more responsibility on organizations to secure their supply chains. ...
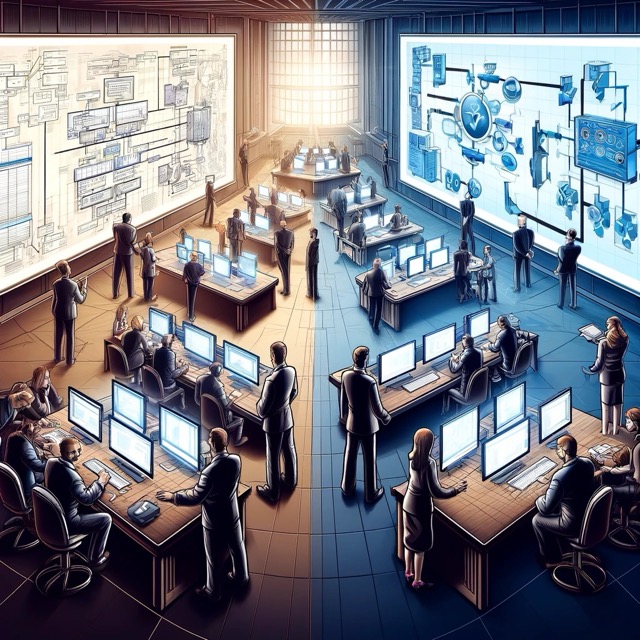
Change Management in Development and Operations
While looking into IT Service Change Management, and primarily in accordance with ITIL, there was one thing that stood out. There seems to be a disconnect between the the development point of view and how change management is implemented by operations. With that I mean that the implementations I have seems to be more applicable for finished product than with software developed in house. The change management processes works when a change is either adding a new product or installing a new version. When it comes to full software development, the change management process gets fuzzy and drawn out. This gets even more distinct when looking at the more agile or DevOps ways of working of development. ...